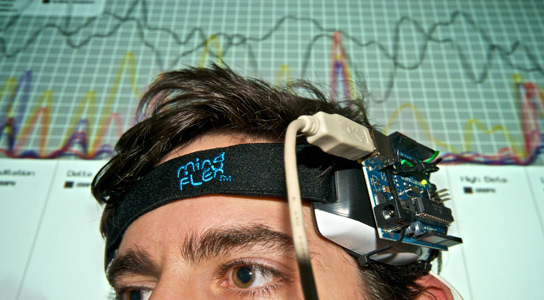
Man wearing EEG headset.
Consumer-grade EEG headsets might be great for gaming, but a new study has found that sensitive personal information, like PIN numbers and credit card data, could be gleaned from the brainwaves of users wearing these headsets.
Researchers presented their findings at the USENIX 2012 Security Symposium 2012. The team of security experts from Oxford, UC Berkeley, and the University of Geneva state that they were able to deduce the digits of PIN numbers, birth months, and areas of residence from subjects wearing the headsets who were presented with images of ATM machines, debit cards, people, maps, and random numbers.

The correct answer was found by the first guess in 20% of the cases for PIN numbers. The location was detected for 30% of the users, and the month of birth for 60%. Researchers presented the subjects with numbers from 0 to 9 randomly. Each number was repeated 16 times over a duration of 90 seconds. The brainwaves were monitored for telltale peaks that would allow the researchers to glean the information.
The EEG headsets are becoming more popular, and affordable. There could be more security risks. The researchers analyzed P300 peaks in the electrical potentials that happened when users are presented with stimuli, which occur 300 milliseconds after an event happens.

The API of these EEG devices provides unrestricted access to the raw EEG signal thanks to the manufacturers’ app stores. These applications have complete control over the stimuli that can be presented to the users.
Potentially, brain spyware could be written by bio-hackers to harvest private information from users, under the guise of a downloaded app. This could happen during a calibration, which is common in these devices.
Reference: “On the Feasibility of Side-Channel Attacks with Brain-Computer Interfaces” by Ivan Martinovic, Doug Davies, Mario Frank, Daniele Perito, Tomas Ros and Dawn Song, USENIX 2012 Security Symposium 2012.
Link








At one point in my life I was worried about implants. Now that just seems silly since…