
A study found that many developing nations are vulnerable to Internet attacks due to reliance on few providers and state-owned transit systems.
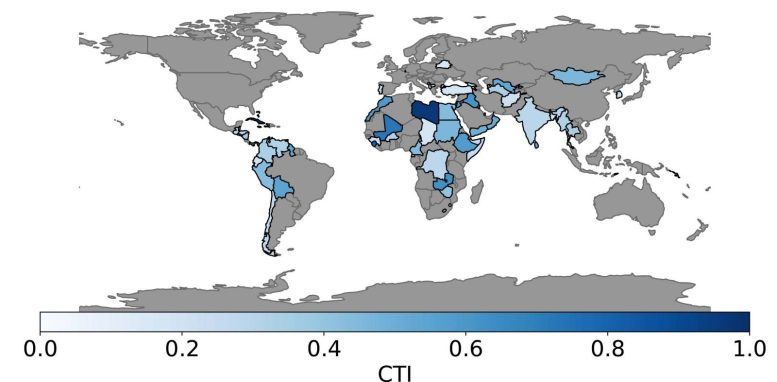
About 25% of the world’s Internet users live in countries that are more vulnerable to targeted attacks on their Internet infrastructure than previously thought. Many of the at-risk countries are located in the Global South, which broadly includes the regions of Latin America, Asia, Africa, and Oceania.
That’s the conclusion of a sweeping, large-scale study conducted by computer scientists at the University of California, San Diego (UCSD). The scientists surveyed 75 countries.
“We wanted to study the topology of the Internet to find weak links that, if compromised, would expose an entire nation’s traffic,” said Alexander Gamero-Garrido, the paper’s first author, who earned his Ph.D. in computer science at UCSD.
Differences in Internet Connectivity Structures
The structure of Internet connectivity differs dramatically in different parts of the world. In many developed countries, such as the United States, a large number of Internet providers compete to provide services for a large number of users. These networks are directly connected to one another and exchange content, a process called direct peering. All the providers can also plug directly into the world’s Internet infrastructure.
“But a large portion of the Internet doesn’t function with peering agreements for network connectivity,” Gamero-Garrido pointed out.
Vulnerability of State-Owned Transit Systems
In other nations, many of them still developing countries, most users rely on a handful of providers for Internet access, and one of these providers serves an overwhelming majority of users. Not only that, but those providers rely on a limited number of companies called transit autonomous systems to get access to the global Internet and traffic from other countries. Researchers found that often these transit autonomous system providers are state-owned.
This, of course, makes countries with this type of Internet infrastructure particularly vulnerable to attacks because all that is needed is to cripple a small number of transit autonomous systems. These countries, of course, are also vulnerable if a main Internet provider experiences outages.
In the worst case scenario, one transit autonomous system serves all users. Cuba and Sierra Leone are close to this state of affairs. By contrast, Bangladesh went from only two to over 30 system providers, after the government opened that sector of the economy to private enterprise.
The Role of Government Regulation and Colonial Legacies
This underlines the importance of government regulation when it comes to the number of Internet providers and transit autonomous systems available in a country. For example, researchers were surprised to find that many operators of submarine Internet cables are state-owned rather than privately operated.
Researchers also found traces of colonialism in the topology of the Internet in the Global South. For example, French company Orange has a strong presence in some African countries.
Researchers relied on Border Gateway Protocol data, which tracks exchanges of routing and reachability information among autonomous systems on the Internet. They are aware that the data can be incomplete, introducing potential inaccuracies, though these are mitigated by the study’s methodology and validation with real, in-country Internet operators.
The next steps include looking at how critical facilities, such as hospitals, are connected to the Internet and how vulnerable they are.
Reference: “Quantifying Nations Exposure to Traffic Observation and Selective Tampering” by Alexander Gamero-Garrido, Esteban Carisimo, Shuai Hao, Bradley Huffaker, Alex C. Snoeren and Alberto Dainotti, 22 March 2022, International Conference on Passive and Active Network Measurement.
DOI: 10.1007/978-3-030-98785-5_29
PDF
Authors: Alberto Dainotti (now at Georgia Institute of Technology), Alexander Gamero-Garrido (now at Northeastern University), Bradley Huffaker and Alex C. Snoeren, University of California San Diego Esteban Carisimo, Northwestern University, Shuai Hao, Old Dominion University
Never miss a breakthrough: Join the SciTechDaily newsletter.
Follow us on Google and Google News.
1 Comment
… this will not be said by me…