
University of Chicago scientists examine vulnerability of smart devices and possible defenses.
As connected devices such as voice assistants, security cameras, and smart appliances grow in popularity, the homes and offices where they are installed become increasingly filled with a dense web of Wi-Fi signals.
A new study from University of Chicago and University of California, Santa Barbara researchers finds that external attackers can use inexpensive technology to turn these ambient signals into motion detectors, monitoring activity inside a building without being detected themselves.
With only a small, commercially available Wi-Fi receiver, an attacker from outside the target site can measure the strength of signals emitted from connected devices and monitor a site remotely for motion, sensing whether a room is occupied. The research, led by leading UChicago computer scientists Heather Zheng and Ben Zhao, reveals the technique of these attacks as well as potential defenses.
“It’s what we call a silent surveillance attack,” said Zheng, a Neubauer Professor of Computer Science at the University of Chicago and expert on networking, security, and wireless technologies. “It’s not just about privacy, it’s more about physical security protection. By just listening to existing Wi-Fi signals, someone will be able to see through the wall and detect whether there’s activity or where there’s a human, even without knowing the location of the devices. They can essentially do a monitoring surveillance of many locations. That’s very dangerous.”
The research builds upon earlier findings that exposed the ability to “see through walls” using Wi-Fi signals. However, previous methods detected indoor activity by sending signals into the building and measuring how they are reflected back to a receiver, a method that would be easy to detect and defend against. The new approach requires only “passive listening” to a building’s existing Wi-Fi signals, does not need to transmit any signals or break encryption, and grows more accurate when more connected devices are present, raising significant security concerns.
“The worrisome thing here is that the attacker has minimal cost, can stay silent without emitting any signal, and still be able to get information about you,” Zheng said.
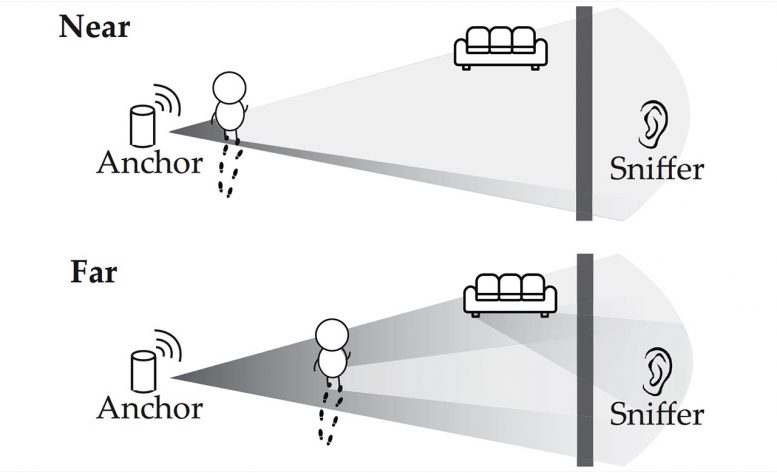
Connected devices typically do not communicate with the internet directly, but do so by regularly transmitting signals to an access point, a hardware device such as a router. When a person walks nearby either device in this conversation, it changes the signal subtly, such that the perturbation can be detected by a nearby receiver “sniffing” the signal. That’s enough information for an observer to know if a person (or large animal, the researchers add) is in the room, with very high accuracy.
Because most building materials do not block the propagation of Wi-Fi signals, the receiver does not even need to be in the same room or building as the access point or connected devices to pick up these changes. These Wi-Fi sniffers are available off the shelf and inexpensive, typically less than $20. They’re also small and unobtrusive, easy to hide near target locations, and passive—sending no signal that could be detected by the target.
“It’s not just about privacy, it’s more about physical security protection.” — Prof. Heather Zheng
The researchers also suggested different methods to block this surveillance technique. One protection would be to insulate buildings against Wi-Fi leakage; however, this would also prevent desirable signals, such as from cellular towers, from entering. Instead, they propose a simple technical method where access points emit a “cover signal” that mixes with signals from connected devices, producing false data that would confuse anyone sniffing for Wi-Fi signatures of motion.
“What the hacker will see is that there’s always people around, so essentially you are creating noise, and they can’t tell whether there is an actual person there or not,” Zheng said. “You can think about it as a privacy button on your access point; you click it on and sacrifice a little bit of the bandwidth, but it protects your privacy.”
Zheng hopes that router manufacturers will consider introducing this privacy feature in future models; some of those firms have announced new features that use a similar method for motion detection, marketed as a home security benefit.
The study also reflects a growing research area in the Department of Computer Science, examining issues around increasingly prevalent connected “Internet of Things” devices. The IoT Security and Privacy Group, which includes Zhao and Zheng and additional faculty members including Nick Feamster, Blase Ur, and Marshini Chetty, will investigate both the benefits and potential vulnerabilities of these technologies, and a new IoT Lab in the Center for Data and Computing provides devices for researchers and students to hack and study for research.
###
Reference: “Et Tu Alexa? When Commodity WiFi Devices Turn into Adversarial Motion Sensors” by Yanzi Zhu, Zhujun Xiao, Yuxin Chen, Zhijing Li, Max Liu, Ben Y. Zhao and Haitao Zheng, Cryptography and Security (cs.CR).
arXiv: 1810.10109
The paper also includes co-authors Zhujun Xiao, Max Liu, and Yuxin Chen of UChicago CS, as well as Yanzi Zhu and Zhijing Li of UCSB.
“Et Tu Alexa? When Commodity WiFi Devices Turn into Adversarial Motion Sensors,” Zhu et al., has been accepted for the Network and Distributed Systems Security (NDSS) symposium in February 2020.
Never miss a breakthrough: Join the SciTechDaily newsletter.
Follow us on Google and Google News.
8 Comments
This is happening to me right now in my own house. Keep on trying to tell my parents but they wont believe me how can I find out who is doing this this a very serious issue. This literary been going on for a year now a bit more. Please to anyone out there please tell me what I can do to track this person down.
I am going thru same thing and at my wits end I have no clue on ho to stop it but it’s literally destroying everything slowly in my life….. Any help????
You say different methods? I’ve looked for info on how to add cover signal as you suggest but have as of yet able to find any specific info on how to go about doing any defensive messer! To stop it ! Would be very helpful if you could give specific sites/ articales/ videos! Or any other form of how to do! I’ve been looking for over a year now!
Dmitri you look to your neighbors ! They have to be close in order to do this attack! Just like mine! Best thing to do is try and find a way to jam/ mitigate the signal! Been years for me!!!! Or get rid of WiFi in the home!!!
Look they have to be close ie next door? Like my neighbors! If you can get rid of WiFi in the home!
THIS IS HAPPENING TO ME, HOW CAN I STOP IT? BERNIE, IRELAND.
Good morning my name is Gladys and I’m going through the same thing. This was a woman they hire someone the guy quit, but I don’t know how she got equipment and it still live in this life four years ago I went to the FBI and they haven’t done nothing finally I found out to the Chicago news how he’s done if you wanna get in touch with me we could talk. My email is there
I’m going to the same thing I need help